Security
North Star's security model is designed for fast finality without sacrificing correctness. It combines three innovations adapted from Cartesi and Fuel Ignition research:
2. ZK Finality
Single-transaction ZK proof — small, cheap, instant to verify
Novel
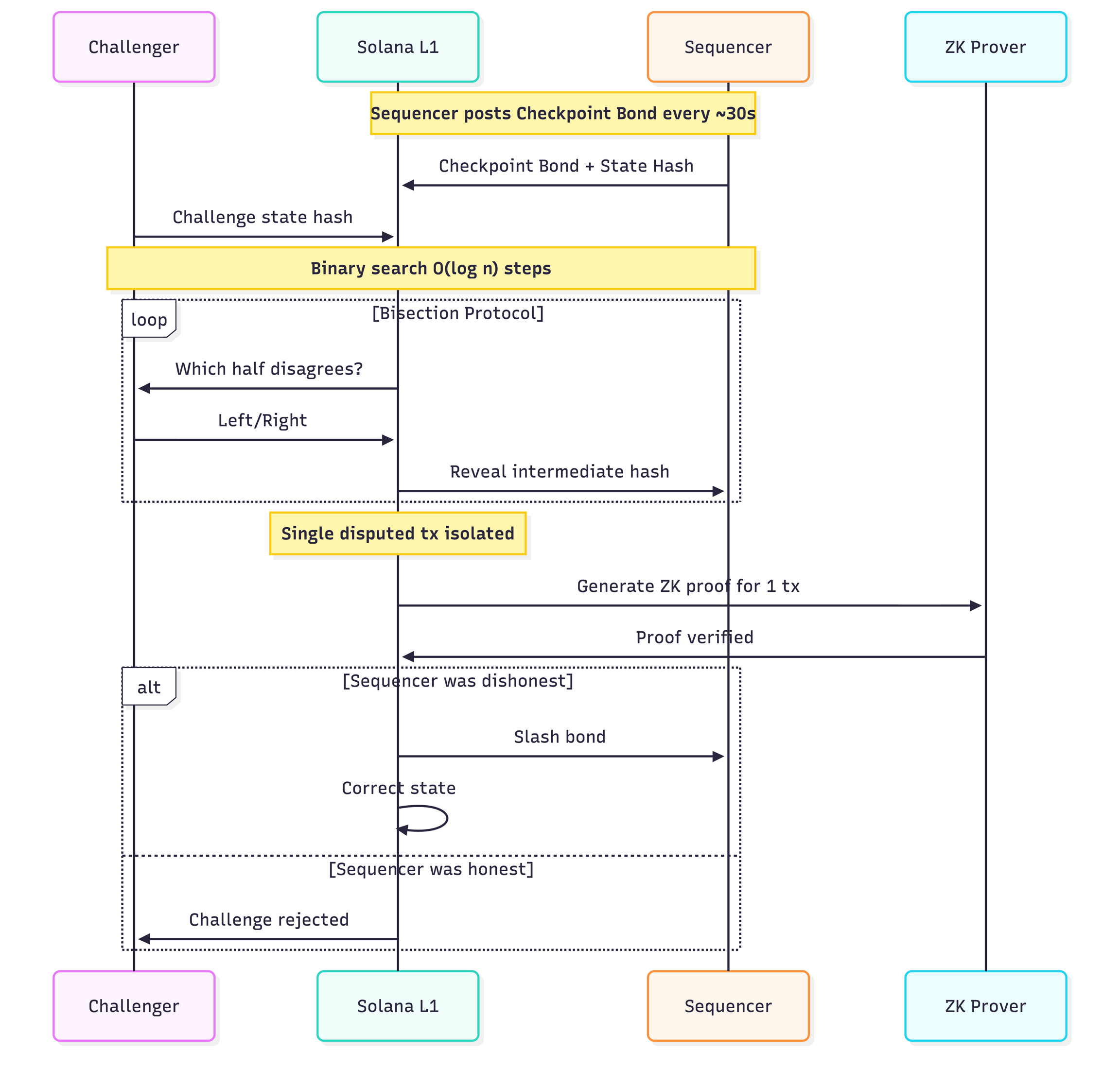
Dispute Game (Bisection Protocol)
Adapted from Cartesi's dispute resolution. When a challenger disagrees with a posted state hash:
Challenger posts a bond and identifies a checkpoint they dispute
Binary search begins: the L1 contract asks "which half of the execution trace do you disagree with?"
In O(log n) rounds (e.g., 20 rounds for 1M transactions), the protocol isolates the single transaction where disagreement occurred
Only ~20 on-chain interactions required regardless of rollup throughput — dramatically cheaper than replaying the entire trace
ZK Finality
Once the bisection protocol isolates the disputed transaction, a ZK proof is generated for that single SVM instruction:
Proof scope: 1 transaction (not the entire batch) — small, fast to generate
Verification: Constant-time on-chain verification via a Solana verifier program
Outcome: If the sequencer's state transition was incorrect, the proof is cryptographically irrefutable → slash the sequencer's bond, correct the state
Accelerated Challenges (Checkpoint Bonds)
Inspired by Fuel Ignition's research on fast-finality optimistic rollups:
Sequencers post a Checkpoint Bond every ~30 seconds alongside the state hash
Bond amount is calibrated to exceed the maximum extractable value from a single checkpoint window
Challenge windows are dynamic — as more validators post checkpoints at higher frequency, the window shrinks. The security assumption: if uncensored validators can submit fraud proofs but do not, the state transitions are valid. Unchallenged checkpoints finalize automatically.
Bisection + ZK verification resolves disputes in minutes, not the 7-day window of traditional optimistic rollups
⏱️ Finality timeline: ~30s checkpoint intervals → dynamic challenge window → dispute resolution in minutes via bisection + ZK. Compare: Ethereum optimistic rollups = 7 days.
Invariant Enforcement
Non-delegated accounts are never writable on the ER — enforced at the SVM runtime level
Delegated accounts are locked on L1 — no L1 transaction can modify them until the session closes
State hashes are computed only over delegated accounts — deterministic and verifiable
Session timeout: if a session exceeds its max duration, the Portal allows forced undelegation
Last updated
